|
This blog post will examine Yachot’s article on internet privacy and iPhone’s legal case with the government.  Many people choose iPhones for their unparalleled privacy. From users to techies Apple has become a brand to depend on. I can remember when the legal showdown began with the government, but Apple’s stand made me pay attention to the brand itself and eventually informed my choice to switch to Apple. I chose this article because it discusses how this case is about the implications of global cybersecurity and basic freedoms. If you want to start a healthy debate, mention that your phone is the best. Android and iPhone users will chime in. What are the real differences between the two when it comes to security and privacy? "One of the primary differences between iOS and Android is the application distribution and vetting models. IOS has a single application store, iTunes, that customers can download applications from. While Apple is not perfect, they have executed better than Google in the application vetting process while attempting to limit malware distribution." (Messmer, 2012) Apple has proven that its security keeps out hackers that seek to find information about people. As the article stated, “But once the government secures a precedent to force a company to vouch for an update that it knows is actually insecure malware, users will stop trusting automatic updates. After all, how would anyone be able to trust an update from Apple when the public knows that the government might be directing the insertion of vulnerabilities into new software, even when it’s signed by Apple?” (Yochot, 2016). Apple isn’t only thinking about unfixed software they are also thinking of the global implications of brokered trust. Apple is uniquely positioned to keep out foreign governments and cybercriminals that protect data and information they collect on all of their users. “Apple rejects the main underlying ethical assumptions detailed here so far. It argues that if it weakened the encryption software so that the government could surveil phones (put in a ‘backdoor’), many millions of people all across the world would lose not just their privacy but also have their security endangered.” (Etzioni, 2018) While Apple has its strengths many people question what Apple does with the data it collects on its users. A trade for cybersecurity. There are some that even criticize the legitimacy of Apple’s claims. “Apple's sandboxing technology restricts iPhone applications to operating system resources with a list of deny/allow rules at the kernel level, but these and other permissions are "way too loose," and "Apple should not claim that an application cannot access data from another application," said Seriot, who works as an iPhone programming trainer at a company called Sen:te.” (Messmer, 2010) However, these criticisms of Apple are outdated as they have proven time and again to be the leaders in an unparalleled system creation. Apple may not be the best tech with the most advancements as competitors are keeping up and somewhat surpassing the company with innovative and new ideas. But Apple still stands out when it comes to the protection of its data and user information. It isn’t Apple people have to be skeptical of, it is in applications where security is compromised. ReferencesEtzioni, A., & Etzioni, A. (2018). Apple: Good Business, Poor Citizen? Journal of Business Ethics, 151(1), 1–11. https://doi.org/10.1007/s10551-016-3233-4
Messmer, E. (2010). Apple iPhone security, privacy claims exaggerated, researcher says; Black Hat presentation discusses iPhone privacy and security mechanisms. Network World. Messmer, E. (2012, December 3). Apple iOS vs. Google Android: It comes down to security; Android seen as more vulnerable but some say its flexibility can mean more security options. Network World, 22. https://link.gale.com/apps/doc/A310686934/AONE?u=tel_a_utl&sid=AONE&xid=c413561b Yochot, N. (2016). 7 Reasons a Government Backdoor to the iPhone Would Be Catastrophic. ACLU. https://www.aclu.org/blog/privacy-technology/internet-privacy/7-reasons-government-backdoor-iphone-would-be-catastrophic
0 Comments
Leave a Reply. |
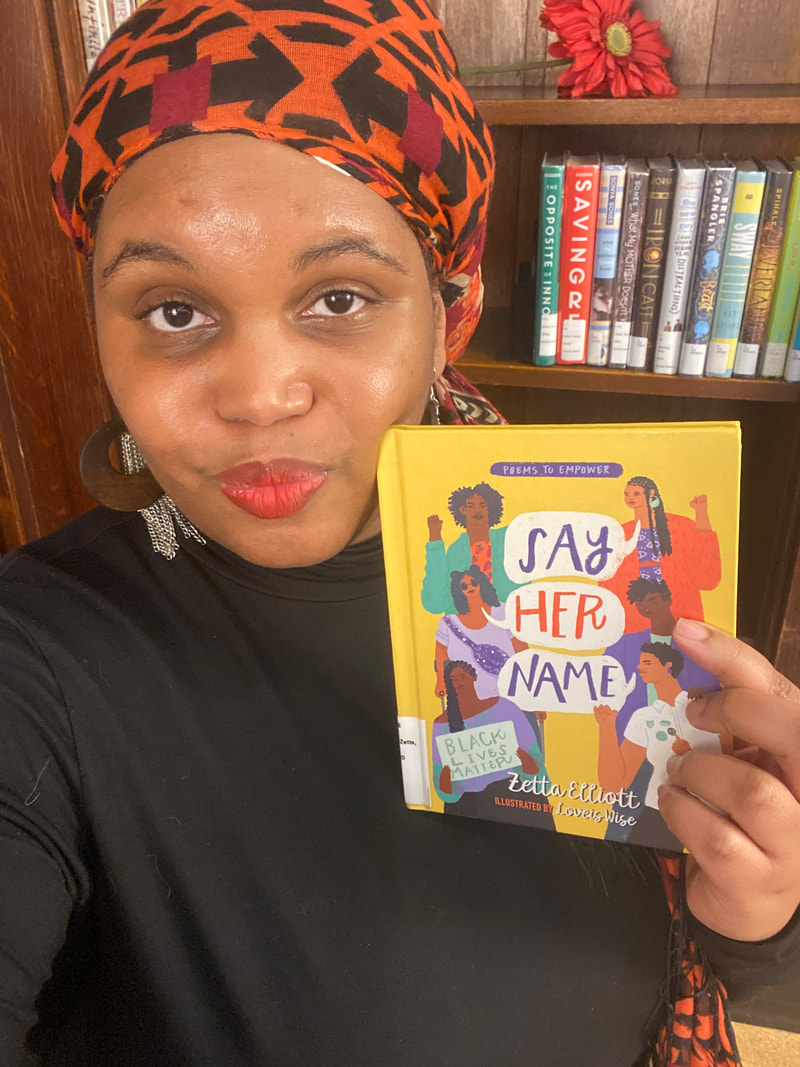
Library SisHey Ya'llI'm Sahara (Sista SOLS) a information professional that has working in public & academic library spaces. Currently, I am a library resident at Clemson University. Here you'll find my residency experience, thoughts on articles, research findings, and story files from what I hope is a fresh perspective. Archives
December 2023
Categories |
 RSS Feed
RSS Feed
